SHA256 is the algorithm that is the basis for mining the first cryptocurrency – Bitcoin. Only specialized ASICs (ASICs) are used for its use.
Currently, new cryptocurrencies are constantly being created on SHA256. Many such coins deserve attention, but a large number of them are frauds. This is confirmed by the fact that they have no official website or community. This article lists all coins on SHA256. History of SHA256 It should be noted that this is a second-generation algorithm based on its predecessor, SHA-1, which was developed in 1995 exclusively for civilian use.
An updated version of the popular algorithm was created by the National Security Agency staff in 2002. Three years later, a patent appeared allowing the algorithm to be used for civilian purposes. The third version of the popular mechanism appeared in 2012, with experts from the National Standards Agency working on its development. With time, SHA-3 has fully replaced its predecessors. Decryption of the transformed data is not possible because the hash value is not considered an encryption process in the classical interpretation of this process.
The one-sided encryption algorithm processes an unlimited amount of information. It is worth noting that all existing versions of the Secure Hashing Algorithm have been designed according to the Merkle-Damgård principle: information is divided into uniform categories. Each group is subjected to one-sided compression, which significantly reduces the length of the data.
This method of encryption has many advantages:
– data compression is performed operatively;
– the conversion process cannot be undone without the keys;
– the probability of collisions is reduced to zero.

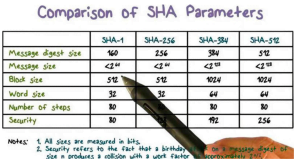
The encryption technology of the SHA-256 protocol is based on a relatively simple cyclic algorithm. This algorithm consists of 64 cycles in which the words are encrypted. The size of each block is 64 bytes and the maximum length of the encrypted code is 33 bytes. The parameters for the message digest are 32 bytes and the word size is usually 4 bytes. The algorithm achieves a speed of 140 Mbit/s.
As already mentioned, the SHA-256 protocol is based on the Merkle-Damgard concept. This means that the data is first divided into blocks and then into individual words. The data goes through 64 or 80 cycles, with each cycle performing a transformation of blocks of words. The resulting hash code is generated by adding the original values.
SHA-256 protocol technical parameters
As this is a technically demanding protocol, it is important to know its main technical parameters. These parameters are listed below:
Block size: 64 bytes Maximum code length: 33 bytes Message digest parameters: 32 bytes Word size: 4 bytes Number of cycles: 64 Algorithm speed: 140 Mbit/s
Coin SHA256
Here is a list of popular cryptocurrencies for SHA256 mining.
We evaluated them based on popularity and network hashing performance. The full list can be found here.
| coins | web | pool |
| Bitcoin (BTC) | bitcoin.org | pool.btc.com F2Pool antpool.com |
| Bitcoin Cash (BCH) | bitcoincash.org | BTC.com bitcoin.com |
| Bitcoin SV (BSV) | bitcoinsv.io | emcd.io viabtc.com |
| DigiByte (DGB) | digibyte.io | F2Pool |
| Syscoin (SYS) | syscoin.org | mining-dutch.nl |
| Namecoin (NMC) | namecoin.org | F2pool |
| Peercoin (PPC) | peercoin.net | ZPOOL Zergpool |
Advantages and disadvantages of the algorithm The main advantage of the SHA256 algorithm is its demand. You can say it a hundred times that this protocol is morally obsolete, but so what? The SHA256 may not be aesthetically pleasing, but it is cheap, reliable and practical. However, there are also disadvantages. First of all, it is a gradual loss of decentralisation. Industrial companies controlled huge data centres and large sums of virtual coins, while small miners were left with crumbs. Alternative crypto-projects are taking measures against ASIC overwriting, but in SHA256 everything is moving at its own pace.
Very low 24-hour trading volume and are very difficult to sell on the exchanges. These cryptocurrencies include
Litecoin Cash (LCC),
Bitcoin Classic (BXC),
Elastos (ELA),
Auroracoin (AUR),
Bitcoin Vault (BTCV),
Super Bitcoin (SBTC),
Pyrk (PYRK),
EmerCoin (EMC),
HTMLCOIN (HTML),
Terracoin (TRC) and Myriad (XMY).
The SHA256 algorithm has many advantages such as its high demand. While this protocol may seem morally outdated, it still remains cheap, reliable and practical. However, there are some disadvantages, such as the gradual loss of decentralisation. Large industrial companies control huge data centres and large amounts of virtual coins, while small miners receive only pennies. Alternative cryptocurrencies are taking measures against the dominance of ASICs, but in the SHA256 algorithm, everything is still largely in the hands of industry players.





